Cozy Bear
Cozy Bear, classified as advanced persistent threat APT29, is a Russian hacker group believed to be associated with Russian intelligence. The Dutch AIVD deduced from security camera footage that it is led by the Russian Foreign Intelligence Service (SVR).[4] Cybersecurity firm CrowdStrike also previously suggested that it may be associated with either the Russian Federal Security Service (FSB) or SVR.[2] The group was given other nicknames by other cybersecurity firms, including Office Monkeys, CozyCar,[5] The Dukes (by Volexity), and CozyDuke[6][7] (by F-Secure).
| Formation | c. 2008[1] |
|---|---|
| Type | Advanced persistent threat |
| Purpose | Cyberespionage, cyberwarfare |
Region | Russia |
| Methods | Spearphishing, malware |
Official language | Russian |
Parent organization | either FSB or SVR[2][3] |
| Affiliations | Fancy Bear |
Formerly called | APT29, Office Monkeys, CozyCar, The Dukes, CozyDuke, Grizzly Steppe (when combined with Fancy Bear) |
Methods and technical capability
Kaspersky Lab determined that the earliest samples of Miniduke are from 2008.[1] The original Miniduke malware was written in assembler.[8] Symantec believes that Cozy Bear had been compromising diplomatic organizations and governments since at least 2010.[9] Cozy Bear appears to have different projects, with different user groups. The focus of its project "Nemesis Gemina" is military, government, energy, diplomatic and telecom sectors.[8]
The CozyDuke malware utilises a backdoor and a dropper. The malware exfiltrates data to a command and control server. Attackers may tailor the malware to the environment.[1] The backdoor components of Cozy Bear's malware are updated over time with modifications to cryptography, trojan functionality, and anti-detection. The speed at which Cozy Bear develops and deploys its components is reminiscent of the toolset of Fancy Bear, which also uses the tools CHOPSTICK and CORESHELL.[10]
Cozy Bear's CozyDuke malware toolset is structurally and functionally similar to second stage components used in early Miniduke, Cosmicduke, and OnionDuke operations. A second stage module of the CozyDuke malware, Show.dll, appears to have been built onto the same platform as OnionDuke, suggesting that the authors are working together or are the same people.[10] The campaigns and the malware toolsets they use are referred to as the Dukes, including Cosmicduke, Cozyduke, and Miniduke.[9] CozyDuke is connected to the MiniDuke and CosmicDuke campaigns, as well as to the OnionDuke cyberespionage campaign. Each threat group tracks their targets and use toolsets that were likely created and updated by Russian speakers.[1] Following exposure of the MiniDuke in 2013, updates to the malware were written in C/C++ and it was packed with a new obfuscator.[8]
Cozy Bear is suspected of being behind the 'HAMMERTOSS' remote access tool which uses commonly visited websites like Twitter and GitHub to relay command data.[11]
Seaduke is a highly configurable, low-profile Trojan only used for a small set of high-value targets. Typically, Seaduke is installed on systems already infected with the much more widely distributed CozyDuke.[9]
Attacks
Evidence suggests that Cozy Bear's targets have included commercial entities and government organizations in Germany, Uzbekistan, South Korea and the US, including the US State Department and the White House in 2014.[10]
Office monkeys (2014)
In March 2014, a Washington, D.C.-based private research institute was found to have Cozyduke (Trojan.Cozer) on their network. Cozy Bear then started an email campaign attempting to lure victims into clicking on a flash video of office monkeys that would also include malicious executables.[9][1] By July the group had compromised government networks and directed Cozyduke-infected systems to install Miniduke onto a compromised network.[9]
In the summer of 2014, digital agents of the Dutch General Intelligence and Security Service infiltrated Cozy Bear. They found that these Russian hackers were targeting the US Democratic Party, State Department and White House. Their evidence influenced the FBI's decision to open an investigation.[4]
Pentagon (August 2015)
In August 2015 Cozy Bear was linked to a spear-phishing cyber-attack against the Pentagon email system causing the shut down of the entire Joint Staff unclassified email system and Internet access during the investigation.[12][13]
Democratic National Committee (2016)
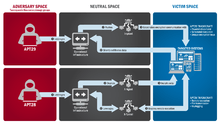
In June 2016, Cozy Bear was implicated alongside the hacker group Fancy Bear in the Democratic National Committee cyber attacks.[2] While the two groups were both present in the Democratic National Committee's servers at the same time, they appeared to be unaware of the other, each independently stealing the same passwords and otherwise duplicating their efforts.[14] A CrowdStrike forensic team determined that while Cozy Bear had been on the DNC's network for over a year, Fancy Bear had only been there a few weeks.[15] Cozy Bear's more sophisticated tradecraft and interest in traditional long-term espionage suggest that the group originates from a separate Russian intelligence agency.[14]
US think tanks and NGOs (2016)
After the 2016 United States presidential election, Cozy Bear was linked to a series of coordinated and well-planned spear phishing campaigns against U.S.-based think tanks and non-governmental organizations (NGOs).[16]
Norwegian Government (2017)
On February 3, 2017, the Norwegian Police Security Service (PST) reported that attempts had been made to spearphish the email accounts of nine individuals in the Ministry of Defence, Ministry of Foreign Affairs, and the Labour Party. The acts were attributed to Cozy Bear, whose targets included the Norwegian Radiation Protection Authority, PST section chief Arne Christian Haugstøyl, and an unnamed college. Prime Minister Erna Solberg called the acts "a serious attack on our democratic institutions."[17] The attacks were reportedly conducted in January 2017.[18]
Dutch ministries (2017)
In February 2017, it was revealed that Cozy Bear and Fancy Bear had made several attempts to hack into Dutch ministries, including the Ministry of General Affairs, over the previous six months. Rob Bertholee, head of the AIVD, said on EenVandaag that the hackers were Russian and had tried to gain access to secret government documents.[19]
In a briefing to parliament, Dutch Minister of the Interior and Kingdom Relations Ronald Plasterk announced that votes for the Dutch general election in March 2017 would be counted by hand.[20]
Operation Ghost
Suspicions that Cozy Bear had ceased operations were dispelled in 2019 by the discovery of three new malware families attributed to Cozy Bear: PolyglotDuke, RegDuke and FatDuke. This shows that Cozy Bear did not cease operations, but rather had developed new tools that were harder to detect. Target compromises using these newly uncovered packages are collectively referred to as Operation Ghost.[21]
In Popular Culture
In the Lair of the Cozy Bear is a translation of the Dutch novel In het hol van de Cozy Bear that relates the story of the infiltration of Cozy Bear told from the perspective of an American liaison officer attached to the Dutch AIVD.
See also
- 2016 United States election interference by Russia
- The Plot to Hack America
References
- "MiniDuke relation 'CozyDuke' Targets White House". Threat Intelligence Times. 27 April 2015. Archived from the original on 11 June 2018. Retrieved 15 December 2016.
- Alperovitch, Dmitri. "Bears in the Midst: Intrusion into the Democratic National Committee". CrowdStrike Blog. Retrieved 27 September 2016.
- https://www.valisluureamet.ee/pdf/raport-2018-ENG-web.pdf
- Huib Modderkolk (25 January 2018). "Dutch agencies provide crucial intel about Russia's interference in US-elections". de Volkskrant.
- "Who Is COZY BEAR?". CrowdStrike. 19 September 2016.
- "F-Secure Study Links CozyDuke to High-Profile Espionage" (Press Release). 30 April 2015. Retrieved 6 January 2017.
- "Cyberattacks Linked to Russian Intelligence Gathering" (Press Release). F-Secure. 17 September 2015. Retrieved 6 January 2017.
- Kaspersky Lab's Global Research & Analysis Team (3 July 2014). "Miniduke is back: Nemesis Gemina and the Botgen Studio". Securelist.
- ""Forkmeiamfamous": Seaduke, latest weapon in the Duke armory". Symantec Security Response. 13 July 2015.
- Baumgartner, Kurt; Raiu, Costin (21 April 2015). "The CozyDuke APT". Securelist.
- "HAMMERTOSS: Stealthy Tactics Define a Russian Cyber Threat Group". FireEye. 9 July 2015. Retrieved 7 August 2015.
- Kube, Courtney (7 August 2015). "Russia hacks Pentagon computers: NBC, citing sources". Retrieved 7 August 2015.
- Starr, Barbara (7 August 2015). "Official: Russia suspected in Joint Chiefs email server intrusion". Retrieved 7 August 2015.
- "Bear on bear". The Economist. 22 September 2016. Retrieved 14 December 2016.
- Ward, Vicky (October 24, 2016). "The Man Leading America's Fight Against Russian Hackers Is Putin's Worst Nightmare". Esquire.
- "PowerDuke: Widespread Post-Election Spear Phishing Campaigns Targeting Think Tanks and NGOs". Volexity. November 9, 2016.
- Stanglin, Doug (February 3, 2017). "Norway: Russian hackers hit spy agency, defense, Labour party". USA Today.
- "Norge utsatt for et omfattende hackerangrep". NRK. February 3, 2017.
- Modderkolk, Huib (February 4, 2017). "Russen faalden bij hackpogingen ambtenaren op Nederlandse ministeries". De Volkskrant (in Dutch).
- Cluskey, Peter (February 3, 2017). "Dutch opt for manual count after reports of Russian hacking". The Irish Times.
- "Operation Ghost: The Dukes aren't back – they never left". ESET Research. October 17, 2019.