XACML
| Paradigm | Declarative programming |
|---|---|
| Designed by | Simon Blackwell |
| Developer | Organization for the Advancement of Structured Information Standards (OASIS) |
| First appeared | April 16, 2001[1] |
| License | OASIS |
| Filename extensions | .xml , .alfa |
| Website | http://oasis-open.org |
| Major implementations | |
| Axiomatics, AuthzForce | |
| Dialects | |
| ALFA (XACML) | |
| Influenced by | |
| XML, SAML | |
| Influenced | |
| ALFA (XACML) | |
XACML stands for "eXtensible Access Control Markup Language". The standard defines a declarative fine-grained, attribute-based access control policy language,[2] an architecture, and a processing model describing how to evaluate access requests according to the rules defined in policies.
As a published standard specification, one of the goals of XACML is to promote common terminology and interoperability between access control implementations by multiple vendors. XACML is primarily an Attribute-Based Access Control system (ABAC), where attributes (bits of data) associated with a user or action or resource are inputs into the decision of whether a given user may access a given resource in a particular way. Role-based access control (RBAC) can also be implemented in XACML as a specialization of ABAC.
The XACML model supports and encourages the separation of the access decision from the point of use. When access decisions are baked into client applications (or based on local machine userids and Access Control Lists (ACLs)), it is very difficult to update the decision criteria when the governing policy changes. When the client is decoupled from the access decision, authorization policies can be updated on the fly and affect all clients immediately.
History
Version 1.0 was ratified by OASIS standards organization in 2003.
Version 2.0 was ratified by OASIS standards organization on February 1, 2005.
The first committee specification of XACML 3.0 was released August 10, 2010.[3] The latest version, XACML 3.0, was standardized in January 2013.[4]
Architecture
Terminology
Non-normative terminology (following RFC 2904, except for PAP)
| Abbr. | Term | Description |
|---|---|---|
| PAP | Policy Administration Point | Point which manages access authorization policies |
| PDP | Policy Decision Point | Point which evaluates access requests against authorization policies before issuing access decisions |
| PEP | Policy Enforcement Point | Point which intercepts user's access request to a resource, makes a decision request to the PDP to obtain the access decision (i.e. access to the resource is approved or rejected), and acts on the received decision |
| PIP | Policy Information Point | The system entity that acts as a source of attribute values (i.e. a resource, subject, environment) |
| PRP | Policy Retrieval Point | Point where the XACML access authorization policies are stored, typically a database or the filesystem. |
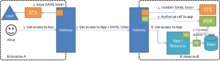
Flow

- A user sends a request which is intercepted by the Policy Enforcement Point (PEP)
- The PEP converts the request into a XACML authorization request
- The PEP forwards the authorization request to the Policy Decision Point (PDP)
- The PDP evaluates the authorization request against the policies it is configured with. The policies are acquired via the Policy Retrieval Point (PRP) and managed by the Policy Administration Point (PAP). If needed it also retrieves attribute values from underlying Policy Information Points (PIP).
- The PDP reaches a decision (Permit / Deny / NotApplicable / Indeterminate) and returns it to the PEP
Policy elements
Structural elements
XACML is structured into 3 levels of elements:
- PolicySet,
- Policy,
- Rule.
A policy set can contain any number of policy elements and policy set elements. A policy can contain any number of rule elements.[5]
Attributes and categories
Policies, policy sets, rules and requests all use subjects, resources, environments, and actions.
- A subject element is the entity requesting access. A subject has one or more attributes.
- The resource element is a data, service or system component. A resource has one or more attributes.
- An action element defines the type of access requested on the resource. Actions have one or more attributes.
- An environment element can optionally provide additional information.
Targets
XACML provides a target,[6] which is basically a set of simplified conditions for the subject, resource, and action that must be met for a policy set, policy, or rule to apply to a given request. Once a policy or policy set is found to apply to a given request, its rules are evaluated to determine the access decision and response.
In addition to being a way to check applicability, target information also provides a way to index policies, which is useful if you need to store many policies and then quickly sift through them to find which ones apply. When a request to access that service arrives, the PDP will know where to look for policies that might apply to this request because the policies are indexed based on their target constraints. Note that a target may also specify that it applies to any request.
Policy set, policy and rule can all contain target elements.
Conditions
Conditions only exist in rules. Conditions are essentially an advanced form of a target which can use a broader range of functions and more importantly can be used to compare two or more attributes together, e.g. subject-id==doctor-id. With conditions, it is possible to implement segregation of duty checks or relationship-based access control.
Obligations
Within XACML, a concept called obligations can be used. An obligation is a directive from the policy decision point (PDP) to the policy enforcement point (PEP) on what must be carried out before or after an access is approved. If the PEP is unable to comply with the directive, the approved access may or must not be realized. The augmentation of obligations eliminates a gap between formal requirements and policy enforcement. An example of an obligation could look like this:
Access control rule:
Allow access to resource MedicalJournal with attribute patientID=x
if Subject match DesignatedDoctorOfPatient
and action is read
with obligation
on Permit: doLog_Inform(patientID, Subject, time)
on Deny : doLog_UnauthorizedLogin(patientID, Subject, time)
The XACML's obligation can be an effective way to meet formal requirements (non-repudiation for example) that can be hard to implement as access control rules. Furthermore, any formal requirements will be part of the access control policy as obligations and not as separate functions, which makes policies consistent and centralization of the IT environment easier to achieve.
Combining algorithms
What happens in XACML if there are two rules (or policies) that contradict each other? Imagine for instance a first rule that would say managers can view documents and a second rule that would say no one can work before 9am. What if the request is about Alice trying to view a document at 8am? Which rule wins? This is what combining algorithms tell us. They help resolve conflicts.
XACML defines a number of combining algorithms[7] that can be identified by a RuleCombiningAlgId or PolicyCombiningAlgId attribute of the <Policy> or <PolicySet> elements, respectively. The rule-combining algorithm defines a procedure for arriving at an access decision given the individual results of evaluation of a set of rules. Similarly, the policy-combining algorithm defines a procedure for arriving at an access decision given the individual results of evaluation of a set of policies.
Functions
Higher Order Functions
The list of higher order functions is as listed below. For a formal definition, refer to the XACML standard.
- anyOf (urn:oasis:names:tc:xacml:3.0:function:any-of)
- parameters: anyAtomicOrBag anyAtomicOrBag*
- return value: boolean
- Description: this function takes in a boolean function and 2 or more attribute values or bags. The higher-order function applies the boolean function to the remaining parameters.
- Example:
anyOf(function[stringEqual], allowedRoles, stringOneAndOnly(role))will return true if (a) role is single-valued, (b) there is at least one value in the attribute bag allowedRoles equal to the value inside the single-valued attribute bag role.
- allOf (urn:oasis:names:tc:xacml:3.0:function:all-of)
- parameters: anyAtomicOrBag anyAtomicOrBag*
- return value: boolean
- anyOfAny (urn:oasis:names:tc:xacml:3.0:function:any-of-any)
- parameters: anyAtomicOrBag anyAtomicOrBag*
- return value: boolean
- allOfAny (urn:oasis:names:tc:xacml:1.0:function:all-of-any)
- parameters: bag[anyAtomic] bag[anyAtomic]
- return value: boolean
- anyOfAll (urn:oasis:names:tc:xacml:1.0:function:any-of-all)
- parameters: bag[anyAtomic] bag[anyAtomic]
- return value: boolean
- allOfAll (urn:oasis:names:tc:xacml:1.0:function:all-of-all)
- parameters: bag[anyAtomic] bag[anyAtomic]
- return value: boolean
- map (urn:oasis:names:tc:xacml:1.0:function:map)
- parameters: anyAtomicOrBag anyAtomicOrBag*
- return value: bag[anyAtomic]
XACML 3.0
Schema
http://docs.oasis-open.org/xacml/3.0/xacml-core-v3-schema-wd-17.xsd
Data types
- http://www.w3.org/2001/XMLSchema#anyURI
- http://www.w3.org/2001/XMLSchema#base64Binary
- http://www.w3.org/2001/XMLSchema#boolean
- http://www.w3.org/2001/XMLSchema#date
- http://www.w3.org/2001/XMLSchema#dateTime
- http://www.w3.org/2001/XMLSchema#dayTimeDuration
- http://www.w3.org/2001/XMLSchema#double
- http://www.w3.org/2001/XMLSchema#hexBinary
- http://www.w3.org/2001/XMLSchema#integer
- http://www.w3.org/2001/XMLSchema#string
- http://www.w3.org/2001/XMLSchema#time
- http://www.w3.org/2001/XMLSchema#yearMonthDuration
- urn:oasis:names:tc:xacml:1.0:data-type:rfc822Name
- urn:oasis:names:tc:xacml:1.0:data-type:x500Name
- urn:oasis:names:tc:xacml:2.0:data-type:dnsName
- urn:oasis:names:tc:xacml:2.0:data-type:ipAddress
- urn:oasis:names:tc:xacml:3.0:data-type:xpathExpression
New in XACML 3.0
New profiles
XACML 3.0 introduces administrative delegation, the JSON Profile of XACML (request/response), the REST Profile of XACML, the Multiple Decision Profile of XACML, and many more.
Delegation
The implementation of delegation is new in XACML 3.0. The delegation mechanism is used to support decentralized administration of access policies. It allows an authority (delegator) to delegate all or parts of its own authority or someone else's authority to another user (delegate) without any need to involve modification of the root policy.
This is because, in this delegation model, the delegation rights are separated from the access rights. These are instead referred to as administrative control policies.[8] Access control and administrative policies work together as in the following scenario:
A partnership of companies' many services are protected by an access control system. The system implements the following central rules to protect its resources and to allow delegation:
Access control rules:
Allow access
to resource with attribute WebService
if subject is Employee and action is read or write.
Administration control rules:
Allow delegation of access control rule #1
to subjects with attribute Consultant.
Conditions:
delegation must expire within 6 months,
resource must not have attribute StrictlyInternal.
(Attributes can be fetched from an external source, e.g. a LDAP catalog.)
When a consultant enters the corporation, a delegation can be issued locally by the consultant's supervisor, authorizing the consultant access to systems directly.
The delegator (the supervisor in this scenario) may only have the right to delegate a limited set of access rights to consultants.
Other features
Other new features of XACML 3.0 are listed at http://www.webfarmr.eu/2010/07/enhancements-and-new-features-in-xacml-3-axiomatics/
The XACML TC is also publishing a list of changes here: http://wiki.oasis-open.org/xacml/DifferencesBetweenXACML2.0AndXACML3.0
Sample Policies
Date & Time-based Authorization in XACML
This rule implements the use-it-lose-it access control paradigm. If a user does not log in for 30 days, then they lose access.
In pseudo-code: deny if currentDateTime > lastLogin + 30 days
<xacml3:Rule RuleId="f6637b3f-3690-4cce-989c-2ce9c053d6fa" Effect="Deny">
<xacml3:Description>Use it or lose it: this policy denies access if lastLogin is more than 30 days away from today's date</xacml3:Description>
<xacml3:Target/>
<xacml3:Condition >
<xacml3:Apply FunctionId="urn:oasis:names:tc:xacml:1.0:function:any-of">
<xacml3:Function FunctionId="urn:oasis:names:tc:xacml:1.0:function:dateTime-greater-than"/>
<xacml3:Apply FunctionId="urn:oasis:names:tc:xacml:3.0:function:dateTime-add-dayTimeDuration">
<xacml3:Apply FunctionId="urn:oasis:names:tc:xacml:1.0:function:dateTime-one-and-only">
<xacml3:AttributeDesignator Category="urn:oasis:names:tc:xacml:1.0:subject-category:access-subject" AttributeId="com.acme.user.lastLogin" DataType="http://www.w3.org/2001/XMLSchema#dateTime" MustBePresent="false"/>
</xacml3:Apply>
<xacml3:AttributeValue DataType="http://www.w3.org/2001/XMLSchema#dayTimeDuration">P30D</xacml3:AttributeValue>
</xacml3:Apply>
<xacml3:AttributeDesignator Category="urn:oasis:names:tc:xacml:3.0:attribute-category:environment" AttributeId="urn:oasis:names:tc:xacml:1.0:environment:current-dateTime" DataType="http://www.w3.org/2001/XMLSchema#dateTime" MustBePresent="false"/>
</xacml3:Apply>
</xacml3:Condition>
</xacml3:Rule>
Time-based Authorization in XACML
This rule grants access if the current time is greater than 9am and less than 5pm.
<xacml3:Rule RuleId="c01d7519-be21-4985-88d8-10941f44590a" Effect="Permit">
<xacml3:Description>Allow if time between 9 and 5</xacml3:Description>
<xacml3:Target>
<xacml3:AnyOf>
<xacml3:AllOf>
<xacml3:Match MatchId="urn:oasis:names:tc:xacml:1.0:function:time-greater-than">
<xacml3:AttributeValue DataType="http://www.w3.org/2001/XMLSchema#time">09:00:00</xacml3:AttributeValue>
<xacml3:AttributeDesignator Category="urn:oasis:names:tc:xacml:3.0:attribute-category:environment" AttributeId="urn:oasis:names:tc:xacml:1.0:environment:current-time" MustBePresent="false" DataType="http://www.w3.org/2001/XMLSchema#time"/>
</xacml3:Match>
</xacml3:AllOf>
</xacml3:AnyOf>
<xacml3:AnyOf>
<xacml3:AllOf>
<xacml3:Match MatchId="urn:oasis:names:tc:xacml:1.0:function:time-less-than">
<xacml3:AttributeValue DataType="http://www.w3.org/2001/XMLSchema#time">17:00:00</xacml3:AttributeValue>
<xacml3:AttributeDesignator Category="urn:oasis:names:tc:xacml:3.0:attribute-category:environment" AttributeId="urn:oasis:names:tc:xacml:1.0:environment:current-time" MustBePresent="false" DataType="http://www.w3.org/2001/XMLSchema#time"/>
</xacml3:Match>
</xacml3:AllOf>
</xacml3:AnyOf>
</xacml3:Target>
</xacml3:Rule>
Sample Requests & Responses
XACML 3.0 Request
<xacml-ctx:Request ReturnPolicyIdList="true" CombinedDecision="false" xmlns:xacml-ctx="urn:oasis:names:tc:xacml:3.0:core:schema:wd-17">
<xacml-ctx:Attributes Category="urn:oasis:names:tc:xacml:3.0:attribute-category:action" >
<xacml-ctx:Attribute AttributeId="actionId" IncludeInResult="true">
<xacml-ctx:AttributeValue DataType="http://www.w3.org/2001/XMLSchema#string">view</xacml-ctx:AttributeValue>
</xacml-ctx:Attribute>
</xacml-ctx:Attributes>
<xacml-ctx:Attributes Category="urn:oasis:names:tc:xacml:3.0:attribute-category:resource" >
<xacml-ctx:Attribute AttributeId="resource-id" IncludeInResult="true">
<xacml-ctx:AttributeValue DataType="http://www.w3.org/2001/XMLSchema#string">doc#123</xacml-ctx:AttributeValue>
</xacml-ctx:Attribute>
</xacml-ctx:Attributes>
<xacml-ctx:Attributes Category="urn:oasis:names:tc:xacml:1.0:subject-category:access-subject" >
<xacml-ctx:Attribute AttributeId="user.identifier" IncludeInResult="true">
<xacml-ctx:AttributeValue DataType="http://www.w3.org/2001/XMLSchema#string">Alice</xacml-ctx:AttributeValue>
</xacml-ctx:Attribute>
</xacml-ctx:Attributes>
</xacml-ctx:Request>
XACML 3.0 Responses
XACML 3.0 Sample Response
<xacml-ctx:Response xmlns:xacml-ctx="urn:oasis:names:tc:xacml:3.0:core:schema:wd-17">
<xacml-ctx:Result>
<xacml-ctx:Decision>NotApplicable</xacml-ctx:Decision>
<xacml-ctx:Status>
<xacml-ctx:StatusCode Value="urn:oasis:names:tc:xacml:1.0:status:ok"/>
</xacml-ctx:Status>
</xacml-ctx:Result>
</xacml-ctx:Response>
XACML 3.0 Sample Response with Obligation
The following contains an Obligation block. Obligations are statements that can be returned along with a decision to enrich the decision flow. In this example, the PEP must log that access was granted.
<xacml-ctx:Response xmlns:xacml-ctx="urn:oasis:names:tc:xacml:3.0:core:schema:wd-17">
<xacml-ctx:Result>
<xacml-ctx:Decision>Permit</xacml-ctx:Decision>
<xacml-ctx:Status>
<xacml-ctx:StatusCode Value="urn:oasis:names:tc:xacml:1.0:status:ok"/>
</xacml-ctx:Status>
<xacml-ctx:Obligations>
<xacml-ctx:Obligation ObligationId="logAccess">
</xacml-ctx:Obligation>
</xacml-ctx:Obligations>
<xacml-ctx:PolicyIdentifierList>
<xacml-ctx:PolicyIdReference Version="1.0">http://www.axiomatics.com/automatic-unique-id/18a9eae9-c92b-4087-b2ac-c5a33d7ff477</xacml-ctx:PolicyIdReference>
</xacml-ctx:PolicyIdentifierList>
</xacml-ctx:Result>
</xacml-ctx:Response>
XACML Implementations
| Name | XACML version | Technology | License | Profiles supported |
|---|---|---|---|---|
| AuthzForce (OW2) / (GitHub) | XACML 3.0 | Java | Open Source | Core, RBAC Profile, Multiple Decision Profile, JSON Profile, REST Profile, Additional Combining Algorithms Profile |
| Axiomatics Policy Server | XACML 3.0 | Java, .NET | Commercial | Core, Multiple Decision Profile, JSON Profile of XACML, Hierarchical Profile of XACML, RBAC profile of XACML, DLP/NAC profile of XACML, Export Control profile of XACML, REST Profile of XACML, ... |
| Balana | XACML 3.0 | Java | Open Source | Core |
| ndg-xacml | XACML 2.0 | Python | Open Source | Core |
| NextLabs Control Center and CloudAz | XACML 3.0 | Java, .Net, JavaScript | Commercial | Core, Multi Decision Profile, JSON and REST Profile, Export Control and Intellectual Property Control Profile of XACML |
| OpenAZ (Apache Incubator, previously AT&T XACML) | XACML 3.0 | Java | Apache 2 | Core, Multiple Decision Profile, JSON Profile of XACML, REST Profile of XACML |
| Oracle Entitlements Server | XACML 3.0 | Java | Commercial | Most |
| Security Policy Tool | XACML 2.0 & 3.0 | Java | Commercial | A Free and Powerful Graphical and Text-Based XACML Editing Tool (XACML 2.0/3.0), ABAC, Workflow, Multilevel Security Profiles |
| SunXACML | XACML 2.0 | Java | Open Source | Core |
| ViewDS Access Sentinel | XACML 3.0 | x-platform C | Commercial | Core, Multiple Decision Profile, REST Profile, REST/JSON Profile, Hierarchical Resource Profile (partial), SAML2 Profile (partial), Core RBAC Profile, Hierarchical RBAC Profile, DLP/NAC Profile (partial), MAP Authorization Profile, IP Control Profile (partial), EC-US Profile, Privacy Profile |
Developer orientation
In 2013 and 2014, the XACML Technical Committee focused on designing new profiles to facilitate developer integration. These include:
- The REST profile of XACML written by Remon Sinnema of EMC
- The JSON profile of XACML written by David Brossard of Axiomatics
- The ALFA profile of XACML written by Pablo Giambiagi, Srijith Nair, and David Brossard of Axiomatics
All three profiles were showcased at the Cloud Identity Summit 2014 in Monterey, California. Using these profiles, integrating fine-grained authorization into applications becomes much easier.
The JSON Profile of XACML
The JSON profile of XACML simplifies the integration between the PEP and the PDP.
Sample JSON request
{
"Request": {
"AccessSubject": {
"Attribute": [
{
"AttributeId": "com.acme.user.employeeId",
"Value": "Alice"
}
]
},
"Resource": {
"Attribute": [
{
"AttributeId": "com.acme.record.recordId",
"Value": "123"
},
{
"AttributeId": "com.acme.object.objectType",
"Value": "record"
}
]
},
"Action": {
"Attribute": [
{
"AttributeId": "com.acme.action.actionId",
"Value": "view"
}
]
},
"Environment": {
"Attribute": []
}
}
}
Sample JSON Response
{
"Response" : {
"Decision" : "Permit",
"Status" : {
"StatusCode" : {
"Value" : "urn:oasis:names:tc:xacml:1.0:status:ok"
}
}
}
}
XACML and Other Standards
XACML and SAML
SAML is an identity SSO and federation standard used for authentication. SAML is used as a common identity token format between different applications. SAML and XACML are both defined by OASIS. SAML and XACML were designed to interoperate where SAML is used to carry identity information / virtual identities and XACML is used to drive the access control logic through policies.
XACML and OAuth
OAuth 2.0 is considered to be an authorization standard. It differs from XACML though in its origin, its purpose, and its applications. OAuth is about:
- delegated access control: I, the user, delegate another user or service access to the resource I own. For instance via OAuth, I grant Twitter (the service) the ability to post on my Facebook wall (the resource).
- handling the password anti-pattern.[9] Whenever you want to integrate 2 services together, in a traditional, legacy model you have to provide service B with your user credentials on service A so that service B can pretend to be you with Service A. This has many risks of course. Using OAuth eliminates the issues with these patterns and lets the user control what service B can do on behalf of the user with service A.
- HTTP-based services / resources
- managing owner (user) approval
XACML does not handle user approval or delegated access or password management. XACML simply provides:
- An access control architecture with the notion of a Policy Decision Point (PDP) as previously discussed and a Policy Enforcement Point (PEP).
- a policy language with which to express a wide range of access control policies including policies that can use consents handled / defined via OAuth.
XACML and OAuth can be combined together to deliver a more comprehensive approach to authorization.
See also
Notes
- ↑ Best, Karl (16 April 2001). "OASIS TC call for participation: XACML". OASIS. Retrieved 31 October 2016.
- ↑ "pure-xacml". www.axiomatics.com. Retrieved 2016-04-27.
- ↑ "XACML 3.0 - committee specification 01". OASIS (oasis-open.org). Retrieved 10 August 2010.
- ↑ eXtensible Access Control Markup Language (XACML) V3.0 approved as an OASIS Standard, eXtensible Access Control Markup Language (XACML) V3.0 approved as an OASIS Standard.
- ↑ http://docs.oasis-open.org/xacml/3.0/xacml-3.0-core-spec-cs-01-en.pdf
- ↑ http://www.oasis-open.org/committees/xacml/
- ↑ "Understanding XACML combining algorithms". www.axiomatics.com. Retrieved 2016-04-27.
- ↑ XACML v3.0 Administrative Policy Version 1.0
- ↑ "OAuth: How It Works". Ping Identity. Retrieved 2016-05-26.
External links
- eXtensible Access Control Markup Language
- XACML for Authorization
- AuthzForce
- HERAS-AF: An open source project providing an XACML-based security framework
- JBoss XACML - Open source LGPL licensed library
- OASIS XACML committee website
- OASIS declaration of issues with two software patents of IBM
- XACML 2.0 PDP and PAP implemented as Axis2 web services
- XACML authorization for many PAM enabled applications
- SunXACML
- EnterpriseJavaXACML
- ZXID http://zxid.org
- OpenAz - Java and C++ Language bindings for XACML with prototypes based on SUN XACML lib
- Xacml4j XACML 2.0 & 3.0 implementation in Java programming language