Evasi0n
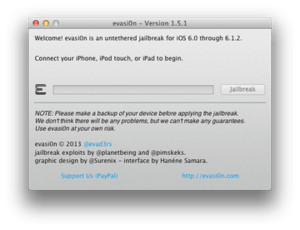 Evasi0n 1.5.1 on OS X | |
| Developer(s) | Evad3rs (pod2g, MuscleNerd, planetbeing, pimskeks) |
|---|---|
| Stable release |
1.5.3
|
| Operating system | Microsoft Windows, OS X and Linux |
| Website |
evasi0n |
| Developer(s) | Evad3rs (pod2g, MuscleNerd, planetbeing, pimskeks) |
|---|---|
| Stable release |
1.0.8
|
| Operating system | Microsoft Windows, and OS X |
| Website |
evasi0n |
Evasi0n, (stylized as "evasi0n"), is a jailbreak program for iOS 6.0 - 6.1.2 and for iOS 7.0 - 7.0.6 (with evasi0n7). It is known for a portable code base and minimal use of arbitrary code execution. More than seven million copies of Evasi0n were downloaded and presumably installed in the first four days after release.[1] It was released on 4 February 2013. Four of the six exploits used were patched by Apple on 18 March 2013 with the release of iOS 6.1.3, which meant the end of the original version of evasi0n. On 22 December 2013, the evad3rs released a new version of evasi0n that supports iOS 7.x, known as evasi0n7. One major exploit used by this jailbreak was patched by Apple with the 4th beta of iOS 7.1 and two more with beta 5. The final release of iOS 7.1 fixed all the exploits used by evasi0n7.[2][3][4]
The evasi0n jailbreak specifically breaches modern security features such as address space layout randomization for kernel space and a version of launchd with a hard-coded list of exclusive services, which serve device stability as well as vendor lock-in on iOS - where Evasi0n reads fixed data vectors to locate the random address of the kernel space and utilizes the /etc/launchd.conf file which launchd processes regardless of the list of exclusive services.[5]
See also
References
- ↑ "Evasi0n 'jailbreaks' 7M iOS devices, update already available for iOS 6.1.1". AppleInsider. 12 February 2013. Retrieved 13 February 2013.
- ↑ "iH8sn0w on Twitter: "So the code sign bug that evasi0n7 uses still exists in 7.1b4. Kernel exploit looks patched though :P"". Twitter.com. 2014-01-21. Retrieved 2015-01-28.
- ↑ "iH8sn0w on Twitter: "Apple fixed the chown vuln that appeared in iOS 7 <http://t.co/65wfTkCKML> and used by evasi0n7 by checking to see if its a symlink again :P"". Twitter.com. 2014-02-04. Retrieved 2015-01-28. External link in
|title=(help) - ↑ "iH8sn0w on Twitter: "evasi0n7's afc sandbox escape is patched in 7.1b5 too."". Twitter.com. 2014-02-04. Retrieved 2015-01-28.
- ↑ Greenberg, Andy. "Inside Evasi0n, The Most Elaborate Jailbreak To Ever Hack Your iPhone". Forbes. Retrieved 23 December 2013.
External links
- Evasi0n.com – official site