cgroups
| Original author(s) | Paul Menage, Rohit Seth |
|---|---|
| Developer(s) | kernel.org (Tejun Heo et al.) and freedesktop.org |
| Initial release | 2007 |
| Written in | C |
| Operating system | Linux |
| Type | System software |
| License | GPL and LGPL |
| Website |
www |
cgroups (abbreviated from control groups) is a Linux kernel feature that limits, accounts for, and isolates the resource usage (CPU, memory, disk I/O, network, etc.) of a collection of processes.
Engineers at Google (primarily Paul Menage and Rohit Seth) started the work on this feature in 2006 under the name "process containers".[1] In late 2007, the nomenclature changed to "control groups" to avoid confusion caused by multiple meanings of the term "container" in the Linux kernel context, and the control groups functionality was merged into the Linux kernel mainline in kernel version 2.6.24, which was released in January 2008.[2] Since then, developers have added many new features and controllers, such as support for kernfs in 2014,[3] firewalling,[4] and unified hierarchy.[5]
Versions
There are two versions of cgroups.
Cgroups was originally written by Paul Menage et al. and mainlined into the Linux kernel in 2007. Afterwards this is called cgroups version 1.[6]
Then development and maintenance of cgroups was taken over by Tejun Heo. Tejun Heo redesigned and rewrote cgroups. This rewrite is now called version 2, the documentation of cgroups-v2 first appeared in Linux kernel 4.5 released on March 14, 2016.[7]
Unlike v1, cgroup v2 has only a single process hierarchy and discriminates between processes, not threads.
Features
One of the design goals of cgroups is to provide a unified interface to many different use cases, from controlling single processes (by using nice, for example) to whole operating system-level virtualization (as provided by OpenVZ, Linux-VServer or LXC, for example). Cgroups provides:
- Resource limiting
- groups can be set to not exceed a configured memory limit, which also includes the file system cache[8][9]
- Prioritization
- some groups may get a larger share of CPU utilization[10] or disk I/O throughput[11]
- Accounting
- measures a group's resource usage, which may be used, for example, for billing purposes[12]
- Control
- freezing groups of processes, their checkpointing and restarting[12]
Use
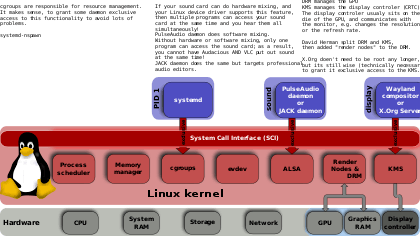
A control group (abbreviated as cgroup) is a collection of processes that are bound by the same criteria and associated with a set of parameters or limits. These groups can be hierarchical, meaning that each group inherits limits from its parent group. The kernel provides access to multiple controllers (also called subsystems) through the cgroup interface;[2] for example, the "memory" controller limits memory use, "cpuacct" accounts CPU usage, etc.
Control groups can be used in multiple ways:
- By accessing the cgroup virtual file system manually.
- By creating and managing groups on the fly using tools like cgcreate, cgexec, and cgclassify (from libcgroup).
- Through the "rules engine daemon" that can automatically move processes of certain users, groups, or commands to cgroups as specified in its configuration.
- Indirectly through other software that uses cgroups, such as Docker, Linux Containers (LXC) virtualization,[13] libvirt, systemd, Open Grid Scheduler/Grid Engine,[14] and Google's developmentally defunct lmctfy.
The Linux kernel documentation contains some technical details of the setup and use of control groups version 1[15] and version 2 [16].
Redesign
Redesign of cgroups started in 2013,[17] with additional changes brought by versions 3.15 and 3.16 of the Linux kernel.[18][19][20]
Namespace isolation
While not technically part of the cgroups work, a related feature of the Linux kernel is namespace isolation, where groups of processes are separated such that they cannot "see" resources in other groups. For example, a PID namespace provides a separate enumeration of process identifiers within each namespace. Also available are mount, UTS, network and SysV IPC namespaces.
- The PID namespace provides isolation for the allocation of process identifiers (PIDs), lists of processes and their details. While the new namespace is isolated from other siblings, processes in its "parent" namespace still see all processes in child namespaces—albeit with different PID numbers.[21]
- Network namespace isolates the network interface controllers (physical or virtual), iptables firewall rules, routing tables etc. Network namespaces can be connected with each other using the "veth" virtual Ethernet device.[22]
- "UTS" namespace allows changing the hostname.
- Mount namespace allows creating a different file system layout, or making certain mount points read-only.[23]
- IPC namespace isolates the System V inter-process communication between namespaces.
- User namespace isolates the user IDs between namespaces.[24]
Namespaces are created with the "unshare" command or syscall, or as new flags in a "clone" syscall.[25]
The "ns" subsystem was added early in cgroups development to integrate namespaces and control groups. If the "ns" cgroup was mounted, each namespace would also create a new group in the cgroup hierarchy. This was an experiment that was later judged to be a poor fit for the cgroups API, and removed from the kernel.
Linux namespaces were inspired by the more general namespace functionality used heavily throughout Plan 9 from Bell Labs.[26]
Unified hierarchy
Kernfs was introduced into the Linux kernel with version 3.14 on March 2014, the main author being Tejun Heo.[27] One of the main motivators for a separate kernfs is the cgroups file system. Kernfs is basically created by splitting off some of the sysfs logic into an independent entity, thus easing for other kernel subsystems the implementation their own virtual file system with handling for device connect and disconnect, dynamic creation and removal, and other attributes. Redesign continued into version 3.15 of the Linux kernel.[28]
Kernel memory control groups (kmemcg)
Kernel memory control groups (kmemcg) were merged into version 3.8 (February 2013, 18) of the Linux kernel mainline.[29][30][31] The kmemcg controller can limit the amount of memory that the kernel can utilize to manage its own internal processes.
Adoption
Various projects use cgroups as their basis, including CoreOS, Docker, Hadoop, Jelastic, Kubernetes,[32] lmctfy (Let Me Contain That For You), LXC (LinuX Containers), systemd, Mesos and Mesosphere,[32] and HTCondor. Major Linux distributions also adopted it such as Red Hat Enterprise Linux (RHEL) 6.0 in November 2010, and 3 years later adoption by the mainline Linux kernel.[33]
See also
- Operating system–level virtualization implementations
- Process group
- Tc (Linux) – a traffic control utility that has slight functional overlap with network-oriented cgroup settings
References
- ↑ Jonathan Corbet (29 May 2007). "Process containers". LWN.net.
- 1 2 Jonathan Corbet (29 October 2007). "Notes from a container". LWN.net. Retrieved 2015-04-14.
The original 'containers' name was considered to be too generic – this code is an important part of a container solution, but it's far from the whole thing. So containers have now been renamed 'control groups' (or 'cgroups') and merged for 2.6.24.
- ↑ "cgroup: convert to kernfs". lkml. 2014-01-28.
- ↑ "netfilter: x_tables: lightweight process control group matching". 23 April 2014. Archived from the original on 24 April 2014.
- ↑ "cgroup: prepare for the default unified hierarchy". 2014-03-13.
- ↑ "diff between Linux kernel 4.4 and 4.5". 2016-03-14.
- ↑ "Documentation/cgroup-v2.txt as appeared in Linux kernel 4.5". 2016-03-14.
- ↑ Jonathan Corbet (31 July 2007). "Controlling memory use in containers". LWN.
- ↑ Balbir Singh, Vaidynathan Srinivasan (July 2007). "Containers: Challenges with the memory resource controller and its performance" (PDF). Ottawa Linux Symposium.
- ↑ Jonathan Corbet (23 October 2007). "Kernel space: Fair user scheduling for Linux". Network World. Retrieved 2012-08-22.
- ↑ Kamkamezawa Hiroyu (19 November 2008). Cgroup and Memory Resource Controller (PDF). Japan Linux Symposium. Archived from the original (PDF presentation slides) on 22 July 2011.
- 1 2 Dave Hansen. Resource Management (PDF presentation slides). Linux Foundation.
- ↑ Matt Helsley (3 February 2009). "LXC: Linux container tools". IBM developerWorks.
- ↑ "Grid Engine cgroups Integration". Scalable Logic. 2012-05-22.
- ↑ "cgroups". kernel.org.
- ↑ https://github.com/torvalds/linux/blob/master/Documentation/admin-guide/cgroup-v2.rst
- ↑ "All About the Linux Kernel: Cgroup's Redesign". Linux.com. 2013-08-15. Retrieved 2014-05-19.
- ↑ "The unified control group hierarchy in 3.16". LWN.net. 2014-06-11.
- ↑ "Pull cgroup updates for 3.15 from Tejun Heo". kernel.org. 2014-04-03.
- ↑ "Pull cgroup updates for 3.16 from Tejun Heo". kernel.org. 2014-06-09.
- ↑ Pavel Emelyanov, Kir Kolyshkin (19 November 2007). "PID namespaces in the 2.6.24 kernel". LWN.net.
- ↑ Jonathan Corbet (30 January 2007). "Network namespaces". LWN.net.
- ↑ Serge E. Hallyn, Ram Pai (17 September 2007). "Applying mount namespaces". IBM developerWorks.
- ↑ Michael Kerrisk (27 February 2013). "Namespaces in operation, part 5: User namespaces". lwn.net Linux Info from the Source.
- ↑ Janak Desai (11 January 2006). "Linux kernel documentation on unshare".
- ↑ "The Use of Name Spaces in Plan 9". 1992.
- ↑ "kernfs, sysfs, driver-core: implement synchronous self-removal". LWN.net. 2014-02-03. Retrieved 2014-04-07.
- ↑ "Linux kernel source tree: kernel/git/torvalds/linux.git: cgroups: convert to kernfs". kernel.org. 2014-02-11. Retrieved 2014-05-23.
- ↑ "memcg: kmem controller infrastructure". kernel.org source code. 2012-12-18.
- ↑ "memcg: kmem accounting basic infrastructure". kernel.org source code. 2012-12-18.
- ↑ "memcg: add documentation about the kmem controller". kernel.org. 2012-12-18.
- 1 2 "Mesosphere to Bring Google's Kubernetes to Mesos". Mesosphere.io. 2014-07-10. Retrieved 2014-07-13.
- ↑ https://access.redhat.com/documentation/en-US/Red_Hat_Enterprise_Linux/6/pdf/6.0_Release_Notes/Red_Hat_Enterprise_Linux-6-6.0_Release_Notes-en-US.pdf
External links
- Linux kernel documentation on cgroups
- Linux kernel Namespaces and cgroups by Rami Rosen
- Namespaces and cgroups, the basis of Linux containers (including cgroups v2), slides of a talk by Rami Rosen, Netdev 1.1, Seville, Spain, 2016
- Understanding the new control groups API, LWN.net, by Rami Rosen, March 2016
- Large-scale cluster management at Google with Borg, April 2015, by Abhishek Verma, Luis Pedrosa, Madhukar Korupolu, David Oppenheimer, Eric Tune and John Wilkes
- Job Objects, similar feature on Windows