Alice and Bob
Alice and Bob are fictional characters commonly used as placeholder names in cryptology, as well as science and engineering literature. The Alice and Bob characters were invented by Ron Rivest, Adi Shamir, and Leonard Adleman in their 1978 paper "A method for obtaining digital signatures and public-key cryptosystems."[1] Subsequently, they have become common archetypes in many scientific and engineering fields, such as quantum cryptography, game theory and physics.[2] As the use of Alice and Bob became more popular, additional characters were added, each with a particular meaning.
Overview
Alice and Bob are the names of fictional characters used for convenience and to aid comprehension. For example, "How can Bob send a private message M to Alice in a public-key cryptosystem?"[1] is believed to be easier to describe and understand than "How can B send a private message M to A in a public-key cryptosystem?"
In cryptography and computer security, Alice and Bob are used extensively as participants in discussions about cryptographic protocols or systems. The names are conventional, and often use a rhyming mnemonic.
History
The first mention of Alice and Bob in the context of cryptography was in Rivest, Shamir, and Adleman's 1978 article "A method for obtaining digital signatures and public-key cryptosystems."[1] They wrote, "For our scenarios we suppose that A and B (also known as Alice and Bob) are two users of a public-key cryptosystem" (p. 121).[1] Previous to this article, cryptographers typically referred to message senders and receivers as A and B, or other simple symbols. In fact, in the two previous articles by Rivest, Shamir, and Adleman, introducing the RSA cryptosystem, there is no mention of Alice and Bob.[3][4]
Within a few years, however, reference to Alice and Bob in cryptological literature became a common trope. Cryptographers would often begin their academic papers with reference to Alice and Bob. For instance, Michael Rabin began his 1981 paper, "Bob and Alice each have a secret, SB and SA, respectively, which they want to exchange."[5] Early on, Alice and Bob were starting to appear in other domains, such as in Manuel Blum's 1981 article, "Coin Flipping by Telephone: A Protocol for Solving Impossible Problems," which begins, "Alice and Bob want to flip a coin by telephone."[6]
Although Alice and Bob were invented with no reference to their personality, authors soon began adding colorful descriptions. In 1983, Blum invented a backstory about a troubled relationship between Alice and Bob, writing, "Alice and Bob, recently divorced, mutually distrustful, still do business together. They live on opposite coasts, communicate mainly by telephone, and use their computers to transact business over the telephone."[7] In 1984, John Gordon delivered his famous "After Dinner Speech" about Alice and Bob, which he imagines to be the first "definitive biography of Alice and Bob."[8]
In addition to adding backstories and personalities to Alice and Bob, authors soon added other characters, with their own personalities. The first to be added was Eve, the "eavesdropper." Eve was invented in 1988 by Charles Bennet, Gilles Brassard, and Jean-Marc Robert, in their paper, "Privacy Amplification by Public Discussion."[9] In Bruce Schneier's book Applied Cryptography, other characters are listed.[10]
Cast of characters
The most common characters are Alice and Bob. Eve, Mallory, and Trent are also common names, and have fairly well-established "personalities" (or functions). The names often use rhyming mnemonics (for example, Eve, "eavesdropper"; Mallory, "malicious"). Other names are much less common, and flexible in use.
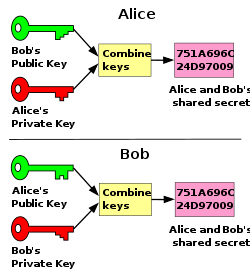
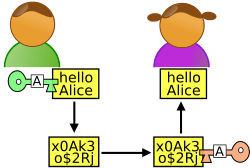
- Alice and Bob. The original, generic characters. Generally, Alice and Bob want to exchange a message or cryptographic key.
- Carol, Carlos or Charlie. A generic third participant.
- Chuck. A third participant, usually of malicious intent.[11]
- Craig. A password cracker, often encountered in situations with stored passwords.
- Dan, Dave or David. A generic fourth participant.
- Erin. A generic fifth participant, but rarely used, as "E" is usually reserved for Eve.
- Eve. An eavesdropper, who is usually a passive attacker. While she can listen in on messages between Alice and Bob, she cannot modify them. In quantum cryptography, Eve may also represent the environment.
- Faythe. A trusted advisor, courier or intermediary. Faythe is used infrequently, and is associated with Faith and Faithfulness. Faythe may be a repository of key service or courier of shared secrets.
- Frank. A generic sixth participant.
- Grace. A government representative. For example, Grace may try to force Alice or Bob to implement backdoors in their protocols. May also deliberately weaken standards.
- Heidi. A mischievous designer for cryptographic standards, but rarely used.[12]
- Judy. A judge who may be called upon to resolve a potential dispute between participants.
- Mallory[13][14][15] or (less commonly) Mallet[16][17][18][19] A malicious attacker. Associated with Trudy, an intruder. Unlike the passive Eve, Mallory/Mallet is an active attacker (often used in man-in-the-middle attacks), who can modify messages, substitute messages, or replay old messages. The difficulty of securing a system against Mallory/Mallet is much greater than against Eve.
- Michael, or Mike. Used as an alternative to the eavesdropper Eve. See Microphone.
- Niaj. Used as an alternative to the eavesdropper Eve in several South Asian nations
- Olivia. An oracle, who provides external data to smart contracts residing on distributed ledger (commonly referred to as blockchain) systems.
- Oscar. An opponent, similar to Mallory, but not necessarily malicious.
- Peggy, or Pat. A prover, who interacts with the system to show that the intended transaction has actually taken place. Peggy is often found in zero-knowledge proofs. Similar to Victor or Vanna.
- Sybil. An pseudonymous attacker, who usually uses a large number of identities. For example, Sybil may attempt to subvert a reputation system. See Sybil attack.
- Trent or Ted. A trusted arbitrator, who acts as a neutral third party.
- Trudy. An intruder.
- Victor,[13] or Vanna.[20] A verifier, similar to Peggy or Pat.
- Walter. A warden, who may guard Alice and Bob.
- Wendy. A whistleblower, who is an insider with privileged access capable of divulging information.
For interactive proof systems there are other characters:
- Arthur and Merlin: Merlin provides answers, and Arthur asks questions. Merlin has unbounded computational ability (like the wizard Merlin). In interactive proof systems, Merlin claims the truth of a statement, and Arthur (like King Arthur), questions him to verify the claim.
- Paul and Carole. Paul asks questions, and Carole provides answers. In the solution of the Twenty Questions problem,[21] "Paul" asked questions (standing in for Paul Erdős) and "Carole" answered them (Carole is an anagram of "oracle"). Paul and Carole were also used in combinatorial games, in the roles of Pusher and Chooser.[22]
- Arthur and Bertha. Arthur is the "Left", "Black", or "Vertical" player, and Bertha is the "Right", "White", or "Horizontal" player in a combinatorial game. Additionally, Arthur, given the same outcome, prefers a game to take the fewest number of moves. Bertha likewise prefers a game to take the most number of moves.[23]
Physics
The names Alice and Bob are also often used to name the participants in thought experiments in physics.[24][25]
See also
References
- 1 2 3 4 Rivest, R. L.; Shamir, A.; Adleman, L. (1978-02-01). "A Method for Obtaining Digital Signatures and Public-key Cryptosystems". Commun. ACM. 21 (2): 120–126. doi:10.1145/359340.359342. ISSN 0001-0782.
- ↑ Newton, David E. (1997). Encyclopedia of Cryptography. Santa Barbara California: Instructional Horizons, Inc. p. 10.
- ↑ Rivest, R. L., A. Shamir, and L. Adleman. “On Digital Signatures and Public-Key Cryptosystems.” Cambridge MA: Massachusetts Institute of Technology, April 1977.
- ↑ Rivest, R. L., A. Shamir, and L. Adleman. Cryptographic Communications System and Method. 4405829. Cambridge MA, filed December 14, 1977, and issued September 20, 1983.
- ↑ Rabin, Michael O. How to exchange secrets with oblivious transfer. Technical Report TR-81, Aiken Computation Lab, Harvard University, 1981.
- ↑ Blum, Manuel. “Coin Flipping by Telephone a Protocol for Solving Impossible Problems.” ACM SIGACT News 15, no. 1 (November 10, 1981): 23–27.
- ↑ Blum, Manuel. “How to Exchange (Secret) Keys.” ACM Trans. Comput. Syst. 1, no. 2 (May 1983): 175–193. doi:10.1145/357360.357368.
- ↑ Gordon, John. “The Alice and Bob After Dinner Speech.” Zurich, April 1984. http://downlode.org/Etext/alicebob.html.
- ↑ Bennett, Charles H., Gilles Brassard, and Jean-Marc Robert. “Privacy Amplification by Public Discussion.” SIAM Journal on Computing 17, no. 2 (April 1988): 210–29. doi:10.1137/0217014.
- ↑ Schneier, Bruce. Applied Cryptography: Protocols, Algorithms and Source Code in C. Hoboken, NJ: John Wiley & Sons, 2015.
- ↑ Tanenbaum, Andrew S. (2007), Distributed Systems: Principles and Paradigms, Pearson Prentice Hall], p. 171;399–402, ISBN 978-0-13-239227-3
- ↑ Fried, Joshua; Gaudry, Pierrick; Heninger, Nadia; Thomé, Emmanuel. "A kilobit hidden SNFS discrete logarithm computation" (PDF). University of Pennsylvania and INRIA, CNRS, University of Lorraine. Retrieved 2016-10-12.
- 1 2 Bruce Schneier (1996), Applied Cryptography: Protocols, Algorithms, and Source Code in C, Second Edition, Wiley, ISBN 9780471117094, p. 23: Table 2.1: Dramatis Personae
- ↑ Szabo, Nick (September 1997). "Formalizing and Securing Relationships on Public Networks". First Monday. 2.
- ↑ Schneier (2010-09-23), Bruce Schneier - Who are Alice & Bob?, retrieved 2017-05-02
- ↑ Bruce Schneier (1994), Applied Cryptography: Protocols, Algorithms, and Source Code in C, Wiley, ISBN 9780471597568, p. 44: "Mallet can intercept Alice's database inquiry, and substitute his own public key for Alice's. He can do the same to Bob."
- ↑ Charles L. Perkins et al. (2000), Firewalls: 24seven, Network Press, ISBN 9780782125290, p. 130: "Mallet maintains the illusion that Alice and Bob are talking to each other rather than to him by intercepting the messages and retransmitting them."
- ↑ Brian LaMacchia (2002), .NET Framework Security, Addison-Wesley, ISBN 9780672321849, p. 616: "Mallet represents an active adversary that not only listens to all communications between Alice and Bob but can also modify the contents of any communication he sees while it is in transit."
- ↑ Shlomi Dolev, ed. (2009), Algorithmic Aspects of Wireless Sensor Networks, Springer, ISBN 9783642054334, p. 67: "We model key choices of Alice, Bob and adversary Mallet as independent random variables A, B and M [...]"
- ↑ Carsten Lund; et al. (1992). "Algebraic Methods for Interactive Proof Systems". J. ACM. ACM. 39 (4): 859–868. doi:10.1145/146585.146605.
- ↑ Spencer, Joel; Winkler, Peter (1992), "Three Thresholds for a Liar", Combinatorics, Probability and Computing, 1 (01): 81–93, doi:10.1017/S0963548300000080
- ↑ Muthukrishnan, S. (2005), Data Streams: Algorithms and Applications, Now Publishers, p. 3, ISBN 978-1-933019-14-7
- ↑ Conway, John Horton (2000). On Numbers and Games. CRC Press. pp. 71, 175, 176. ISBN 9781568811277.
- ↑ "Alice and Bob communicate without transferring a single photon - physicsworld.com". physicsworld.com. Retrieved 2017-06-19.
- ↑ Frazier, Matthew; Taddese, Biniyam; Antonsen, Thomas; Anlage, Steven M. (2013-02-07). "Nonlinear Time Reversal in a Wave Chaotic System". Physical Review Letters. 110 (6). arXiv:1207.1667. Bibcode:2013PhRvL.110f3902F. doi:10.1103/physrevlett.110.063902.
External links
- History of Alice and Bob
- A Method for Obtaining Digital Signatures and Public-Key Cryptosystems
- The Alice and Bob After-Dinner Speech, given at the Zurich Seminar, April 1984, by John Gordon
- Geek Song: "Alice and Bob"
- Alice and Bob jokes (mainly Quantum Computing-related)
- A short history of Bobs (story and slideshow) in the computing industry, from Alice & Bob to Microsoft Bob and Father of Ethernet Bob Metcalfe
- XKCD #177: Alice and Bob